Forum Replies Created
-
AuthorPosts
-
January 31, 2019 at 1:34 pm in reply to: VirtNet does not install on Windows 10 version 1809 x64 #10622
Small update:
Signing VirtNet driver with EV certificate did not help, installation fails with the same error. So it looks that the problem is not related to driver signing and there is another reason for this. Right now it is difficult to say what has changed in 1809, may be Microsoft by chance or by purpose has dropped the support of the legacy versions of NDIS. I hope NDIS 6.0 version of VirtNet may help here…
January 27, 2019 at 10:10 pm in reply to: VirtNet does not install on Windows 10 version 1809 x64 #10619I’ve installed and tested 1809 during the weekend and I confirm that the problem exists. Probably it is related to driver signing policy changes or another possibility is legacy NDIS versions support (for compatibility across all Windows versions VirtNet followed NDIS 3.0 specification). But no worries, I’ll prepare the new build when have some spare time over the next week.
January 20, 2019 at 9:12 am in reply to: VirtNet does not install on Windows 10 version 1809 x64 #10617Thank you for the information. I suspect this is related to the driver signing policy in 1809 update. I will check, probably needed to sign the driver with EV certificate.
It is possible for two applications to use the driver if they filter over different network adapters. Otherwise they may conflict.
However, please note that file handle is normally valid inside the process and can’t be passed outside as it is, unless it is inherited by child process or duplicated (DuplicateHandle). Besides this, please note that handle returned by OpenFilterDriver is a pointer to in-process memory object and can’t be passed by inheritance or duplication.
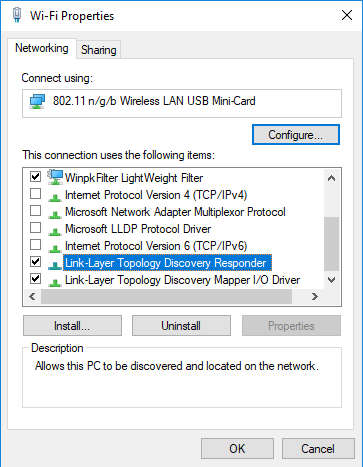
I had some time over the weekend to play with with bridging WiFi and one of the possibilities is enabling Link Layer Discovery Protocol, with the configuration below Wi-Fi adapter without IP address was successfully bridged to the wired network:
Very interesting, thank you for sharing!
Hmm, interesting case. I don’t have a quick answer because I have never tried this kind of setup. If I have some spare time over the weekend I will give it a try.
For the sample code you can check the Ethernet Bridge source where promiscuous mode is used:
Check the line 208 in https://github.com/wiresock/ndisapi/blob/master/examples/ethernet_bridge/EthernetBridge.cpp
I have had one recent similar report regarding Windows 10 Enterprise. And it may happen that Microsoft has reinforced driver signing requirements for the Enterprise editions of Windows (code signing certificate expiry is validated against the install date instead signing date). Will check when have some spare time.
The driver is production signed, so you should not have digital signature problems with installing it. Do you use the driver build from amd64 folder?
What is the version of Windows you use?
Driver version returned by CNdisApi::GetVersion() is: 34025472
In hex this is 0x02073000 or version 3.2.7.
And if NDISAPI returns this value then it definitely means that driver is loaded!
Source code for latest version of ndisapi with a couple of new samples is now available on Github. I’ve just tested dnstracer with and and without WinpkFilter driver installed and availability of the driver was reported properly (so the calls to CNdisApi::IsDriverLoaded worked correct).
What was the Windows version you have tested? I’m not sure, but if you use NCF_HIDDEN attribute for your driver build then it may also affect netcfg output.
block the list of ip addresses which is ddosing us
WinpkFilter built-in filters allow IP address based blocking.
You could use WinpkFilter library to redirect UDP packets for processing in user mode and pass everything else. In your application you can implement any sort of analyses for redirected UDP (including sub string search and etc. ) packets and decide to block/pass or even modify them.
-
AuthorPosts
